All Things Cybersecurity at Your Fingertips.

Cloud Security Breaches
Jul 25, 2024
Introduction Cloud security breaches involve unauthorized access or exposure of sensitive data stored in cloud environments, often due to...

A Deep Dive into Microsoft Azure Security Tools
Jul 16, 2024
Introduction As businesses increasingly migrate to the cloud, ensuring robust security becomes paramount. Microsoft Azure offers a suite of powerful...

Introduction to AWS Config
Jun 24, 2024
What is AWS Config? AWS Config is a service provided by Amazon Web Services (AWS) that helps customers assess, audit, and monitor their AWS resources...
What is XDR (Extended Detection and Response)? An In-Depth Look
Jun 18, 2024
Introduction No organization - especially those with limited cybersecurity expertise and/or bandwidth - can prevent attackers from getting into their...
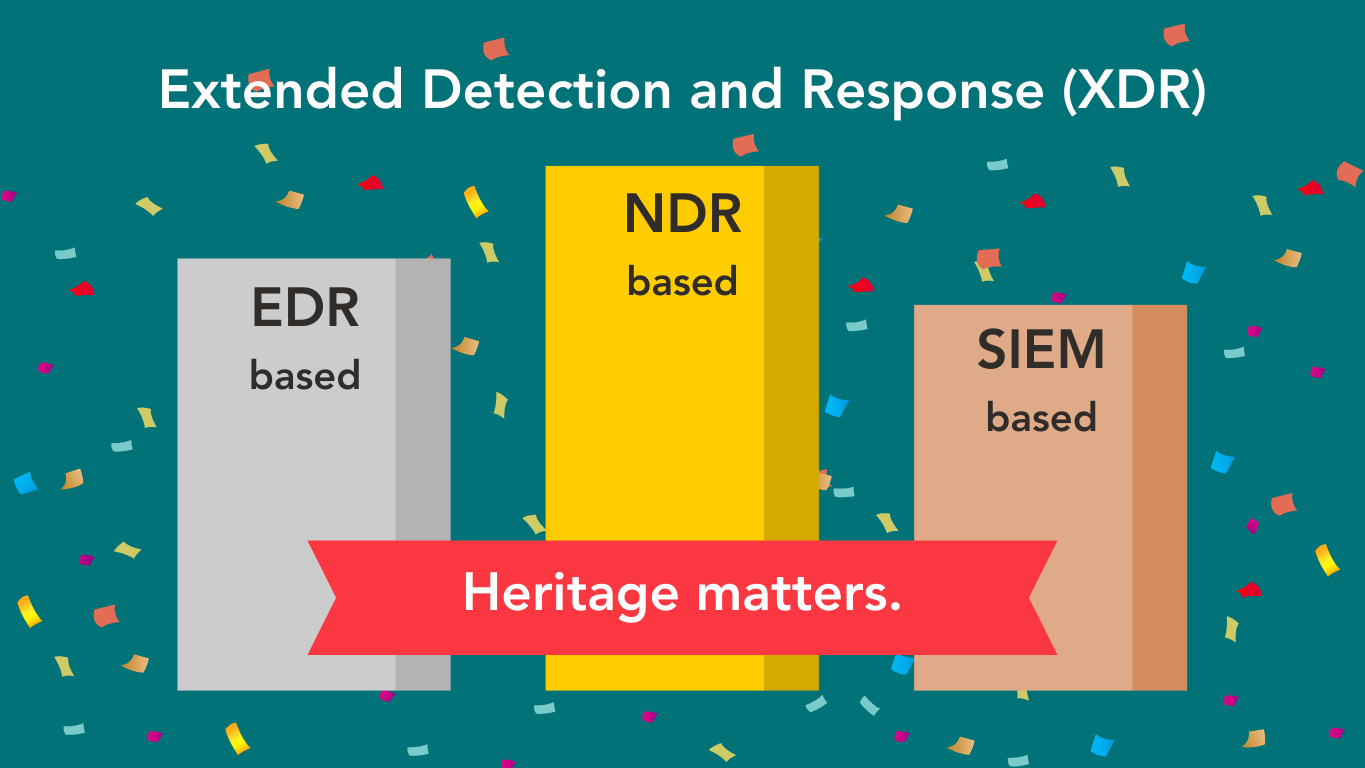
The Cornerstone of XDR: Why NDR is So Essential
Jun 06, 2024
Introduction One of the questions we are most often asked is “What makes Gradient Cyber’s MXDR solution different and better?” We love this question,...

How to Log your VPC queries with Route 53
May 10, 2024
Amazon Route 53, an Amazon Web Services (AWS) offering, simplifies the management of domain names and their association with online resources. It...

Securing Your Cloud Infrastructure with Azure Security Center
Apr 19, 2024
Introduction Data security is critical in today's cloud-based world. Businesses are increasingly moving to the cloud, but this also exposes them to...
Bridging the Talent Gap: MXDR Solves Top 3 Pain Points for IT Security
Mar 13, 2024
A recent study by the Information Systems Audit and Control Association (ISACA) found that 62% of cybersecurity teams were understaffed. That isn’t...

Interesting Insights from Dr. Brian Brown at TCEA 2024
Mar 07, 2024
I had the good fortune to attend the 2024 Texas Computer Education Association (TCEA) event here at the Austin Convention Center last month. Gradient...

A Deep Dive into IAM Access Analyzer: Enhancing AWS Security
Feb 12, 2024
Introduction Are you aware of who is gaining access to your resources? If you're uncertain, it's likely time to reassess your IAM policies. IAM...
Gradient Cyber Adds Azure Protection to its MXDR Solution
Feb 11, 2024
We’re happy to announce that our Managed Detection and Response (MXDR) solution now includes protection for Microsoft Azure workloads and...

Mastering Data Retention & Security: Amazon S3 Object Lifecycle Management
Jan 19, 2024
Introduction As mid-market organizations move applications and workloads to AWS, the specifics of how to handle cloud-based data become critical....

What is MXDR (Managed XDR)? An In-Depth Look
Jan 17, 2024
Introduction In the complex world of cybersecurity, where threats evolve with dizzying speed and complexity, the need for advanced, integrated...
AI in Cybersecurity: Revolutionizing MXDR - Insights from Gradient Cyber
Jan 16, 2024
Understanding MXDR in the Age of AI Managed Extended Detection and Response (MXDR) is a critical defense mechanism against increasingly sophisticated...